The Strategist's Guide to Rapid7: Navigating from Vulnerability Management to Exposure Management
Five Strategic Moves to Dominate the Next Generation of Security Risk Management
In Part 1 of this series, we explored why traditional vulnerability management is stretching beyond its roots. We saw how simply generating lists of CVEs to patch is no longer enough in an era of cloud, DevOps, and sophisticated threats. In Part 2, we focus on Rapid7 -- examining how this security vendor fits into the evolving exposure management landscape, its competitive position, and strategic opportunities to seize the moment.
From Vulnerabilities to Exposures: The New Security Paradigm
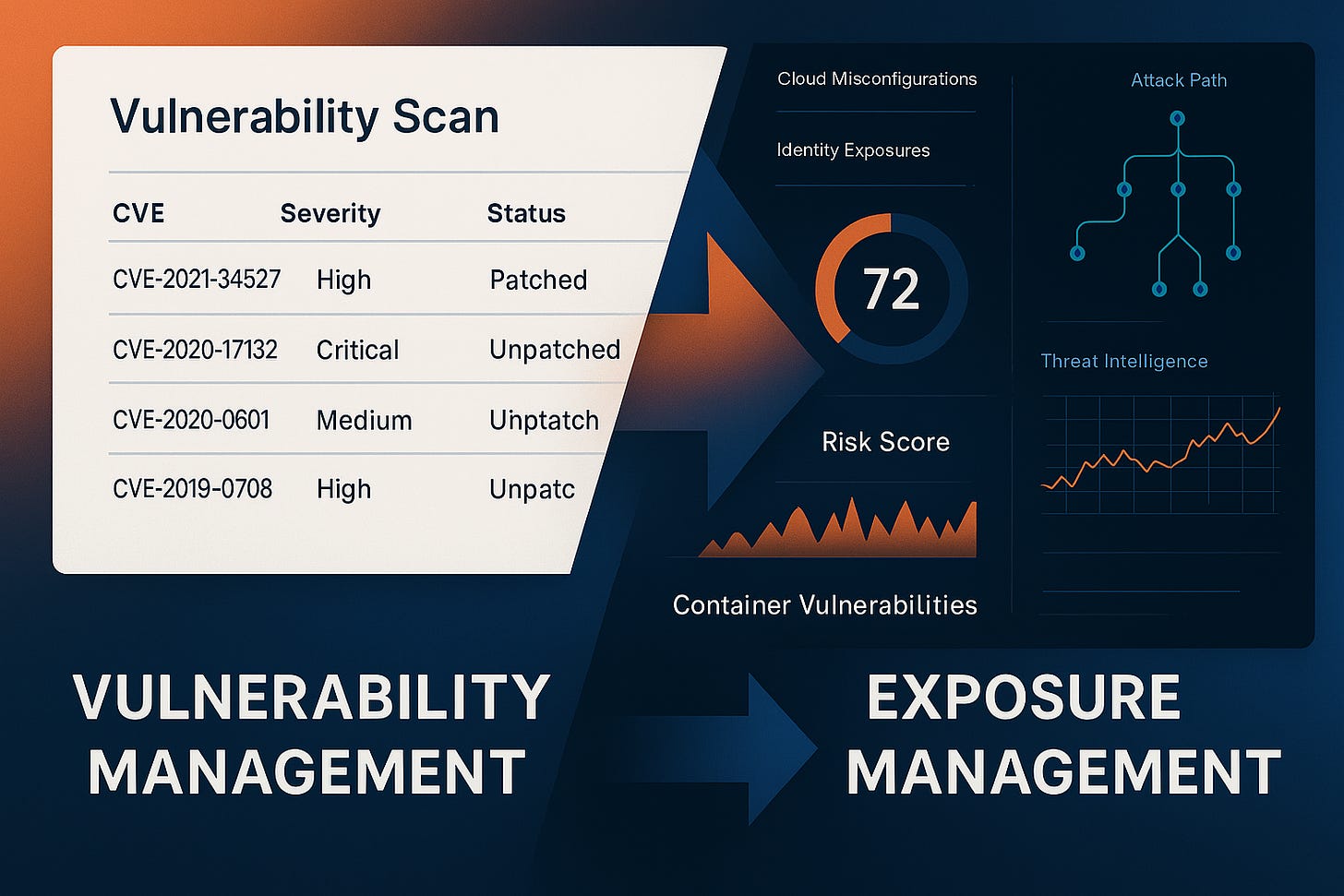
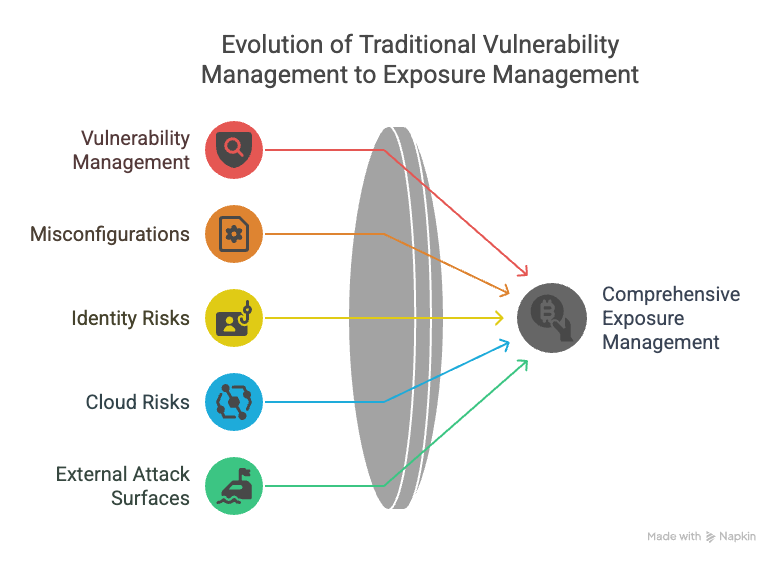
Traditional vulnerability management meant periodically scanning IT assets for known flaws and patching them on a cycle. It was reactive, focusing narrowly on servers and software. But today's threat landscape demands more. Cloud infrastructure, containerized apps, remote work, and shadow IT have exploded the number of potential weaknesses -- many of which aren't traditional "vulnerabilities" at all. Misconfigured cloud storage, exposed credentials, unchecked privileges, and third-party components can all expose an organization to attack even if no CVE is involved.
Leading analysts now advocate for Exposure Management as the next evolution. This approach continuously looks across all assets (on-prem, cloud, IoT), combining vulnerabilities and other risk factors (misconfigurations, identity issues, shadow IT) into a comprehensive risk picture. The goal? Proactive attack surface reduction—managing everything that could be exploited, not just known software bugs.
Rapid7's Position in 2025: SWOT Analysis
Rapid7, known for its InsightVM solution, has been evolving its portfolio to keep pace with this broader vision. Let's examine their current position:
Strengths
Unified Security Platform: Rapid7 has built a well-regarded platform extending beyond vulnerability scanning, with integrated SIEM/XDR (InsightIDR) and cloud security (InsightCloudSec)
Risk-Based Prioritization: Their Active Risk Score (0-1000) incorporates exploit intel, malware exposure, and asset criticality
User-Friendly Interface: Widely praised for intuitive design and reporting, a differentiator against competitors' more complex UIs
Security Research Heritage: Ownership of Metasploit and community-driven research (AttackerKB, Project Sonar) feeds threat intelligence
Broad Ecosystem: Connects with cloud services, ITSM tools, CI/CD pipelines, and can even ingest data from competitors' scanners
Weaknesses
Market Perception: Often viewed as the smaller #3 player behind Tenable and Qualys in large enterprises
Split Focus: Attention is divided across multiple security domains, while competitors focus more exclusively on VM
Feature Catch-Up: Historically lagged in areas like agentless cloud scanning and container/IaC scanning, though acquisitions have helped close gaps
Pricing Structure: Traditional asset-count tiers felt less flexible than competitors' licensing, particularly for smaller organizations
Integration Execution: Challenge of truly unifying acquired technologies into a seamless experience
Opportunities
Platform Convergence: Lead the industry trend toward consolidation of vulnerability management, cloud security, and detection/response
AI-Powered Analytics: Leverage decades of vulnerability and attacker data to train ML models for predictive risk scoring
Workflow Integration: Position as the central hub for exposure data by deepening integrations with existing tools
Adjacent Markets: Extend exposure management to OT/industrial systems, IoT, and expand managed services offerings
Threats
Aggressive Competitors: Tenable and Qualys are pushing unified platforms (Tenable One, etc.) with AI capabilities
Cloud-Native Upstarts: Vendors like Wiz and Orca Security are offering easy cloud scans with vulnerability discovery
Ecosystem Players: Endpoint protection vendors bundling vulnerability assessment into their platforms
Market Consolidation: Potential for major tech players to acquire competitors and shift the landscape
Strategic Recommendations for Rapid7
As Rapid7 continues its evolution from vulnerability management to exposure management, I recommend five strategic areas to focus on:
1. Double Down on AI-Driven Risk Prioritization
Enhance Rapid7's already solid risk-scoring model with predictive machine learning algorithms trained on its vast dataset of vulnerability patterns, exploit trends from Metasploit, and internet scans from Project Sonar. This intelligence could predict which newly disclosed vulnerabilities are likely to be exploited next, or which misconfigurations present the highest imminent risk.
Rapid7 should incorporate an AI assistant within InsightVM that lets users ask questions in natural language: "Which vulnerabilities should I fix first on my critical servers?" or "Explain the impact of CVE-2025-1234 on our environment." The company's recent introduction of AI-generated vulnerability scoring shows they're on this path, but they should accelerate to stay ahead of competitors like Tenable, who are rolling out similar capabilities.
The goal should be transforming the platform from a data source into a decision-support system that augments human analysts - using AI to triage noise, highlight critical issues, suggest remediation steps, and generate executive-friendly summaries.
2. Build a "Universal VM" Connector Ecosystem
Position Rapid7's platform as the central hub for all vulnerability and risk data by expanding third-party integrations and data connectors. They've already taken steps to build connectors to import scan results from Tenable and Qualys. This strategy should continue by making it easy to bring in data from cloud provider scanners, container image scanners, code analysis tools, and more.
Deeper two-way integrations with workflow tools like ServiceNow, Jira, Teams, and Slack will streamline remediation processes. For example, tickets with vulnerability details can be auto-created and their status tracked back in Rapid7, or updates from IT teams can flow into the risk dashboard.
This approach turns Rapid7 into the nerve center for exposure management, even for organizations using multiple scanners. This openness becomes a competitive advantage, showing confidence while reducing barriers for new customers who can try Rapid7 as an overlay before fully switching.
3. Deepen DevSecOps Integration
As IT shifts to the cloud and software is released continuously, Rapid7 must bring vulnerability management closer to development and cloud workflows. This means fully integrating cloud asset scanning into the core VM product, providing one dashboard for both on-prem vulnerabilities and cloud exposures.
Support for containers and Infrastructure-as-Code (IaC) scanning should be enhanced, as these are now fundamental parts of modern stacks. Integrations with CI/CD tools would allow security checks to run automatically as code is checked in or built, catching issues early.
This shift-left approach embeds exposure management into development, focusing on speed - developers deploy to cloud in minutes, so waiting for a weekly scan is too slow. Rapid7 should differentiate by being developer-friendly: offering API-driven scans, plugins for dev tools, and even remediation-as-code suggestions.
4. Unify the Platform Experience
Rapid7's vision of a unified "Command Platform" should remain a strategic focus. All products—InsightVM, InsightIDR, InsightCloudSec, Threat Command, InsightAppSec—need to work seamlessly as one cohesive experience, not just in branding but also in functionality.
This unification enables powerful use cases. Imagine an analyst investigating an alert in Rapid7's SIEM immediately seeing if the affected host has unpatched critical vulnerabilities. Or from the VM side, seeing whether there have been any intrusion alerts related to a particular vulnerability, understanding how actively it's being targeted.
A unified platform simplifies user management, reporting, and deployment while showing combined risk scores across internal and external exposure, threat activity, and asset value. This approach also serves as a defensive moat - customers adopting multiple parts of the Rapid7 platform become stickier as it's harder to replace an integrated ecosystem.
5. Embrace Flexible Pricing Models
Rapid7 should continue innovating in how it packages and prices its services. The company has started with tiered "Command" packages that bundle various features at a platform level, aligning pricing with value delivered rather than individual product fees.
I recommend fully embracing simple, asset-based licensing where customers pay based on the assets covered, regardless of which scanning modules are applied. This reduces friction and encourages utilizing the full platform capabilities without complex add-on fees.
Packaging managed services or extra support with products can further differentiate Rapid7, especially for resource-constrained organizations. Marketing bundles like "InsightVM + Managed Service" or cross-product managed offerings can drive subscription revenue while deepening customer loyalty.
Flexibility in licensing, such as consumption-based pricing for highly elastic cloud environments, could attract cloud-native customers who prefer usage-based models. By simplifying SKUs and offering "all you can eat" feature bundles, Rapid7 can remove buying friction and strengthen its consolidation pitch.
The Road Ahead
Rapid7 is well-positioned to transform from a trusted vulnerability management provider into a leader in the broader exposure management movement. Their integrated platform, risk-focused analytics, and community trust provide a strong foundation.
But capitalizing on this evolving market requires staying aggressive on innovation and extremely responsive to customer needs. The recent Command Platform launch, AI-powered scoring, and cloud risk integration show Rapid7 knows what needs to be done.
The key will be execution - turning vision into reality without losing the simplicity and customer-centric ethos that made Rapid7 successful. By following through on these strategies, Rapid7 can not just ride the wave of exposure management but help define its future.
In the next part of the multiseries post, we will explore Tenable in depth.